Stumbled upon some weird behavior on your Mac and wondering if it’s a rootkit? I caught my eye digging into this recently, and the current state of Mac rootkit detection is…honestly not what you’d expect coming from Windows.
Here’s the reality: there are no reliable dedicated rootkit detectors for macOS. Unlike Windows, which has multiple specialized scanners, Mac users are working with very limited options.
This isn’t Apple being secretive, it’s just how the ecosystem evolved.
A rootkit gives someone remote administrator control over your computer without your knowledge. Once they’re in, they can spy on you or make any changes they want.
The tricky part is that rootkits are designed to hide from the very tools meant to detect them.
Mac Rootkit Detection: What Actually Works on macOS
Before we dive into third-party tools, let’s talk about your best defense: keeping macOS updated. Apple’s security updates remove known malware and rootkits automatically.
This isn’t sexy, but it’s more effective than any scanner.
Go to System Settings > General > Software Update on macOS and install any available updates. Apple’s built-in XProtect and Gatekeeper work in the background, but they’re prevention-focused, not detection tools.
Best Mac Rootkit Scanner Tools (Limited Options)
If you suspect an infection, here are the limited options available (and why they’re not great):
Malwarebytes for Mac (Version 4.6.2)
The most user-friendly option, though it’s not specifically a rootkit detector. Malwarebytes focuses on general malware and adware rather than sophisticated rootkits.
You can try the free version, but honestly if a rootkit has taken hold, general malware scanners often miss them. That’s the fundamental problem we’re dealing with here.
KnockKnock (Version 3.0.1)
This free tool identifies persistent applications that could be rootkits. It’s not a rootkit scanner per se, but it can spot suspicious software that shouldn’t be running at startup.
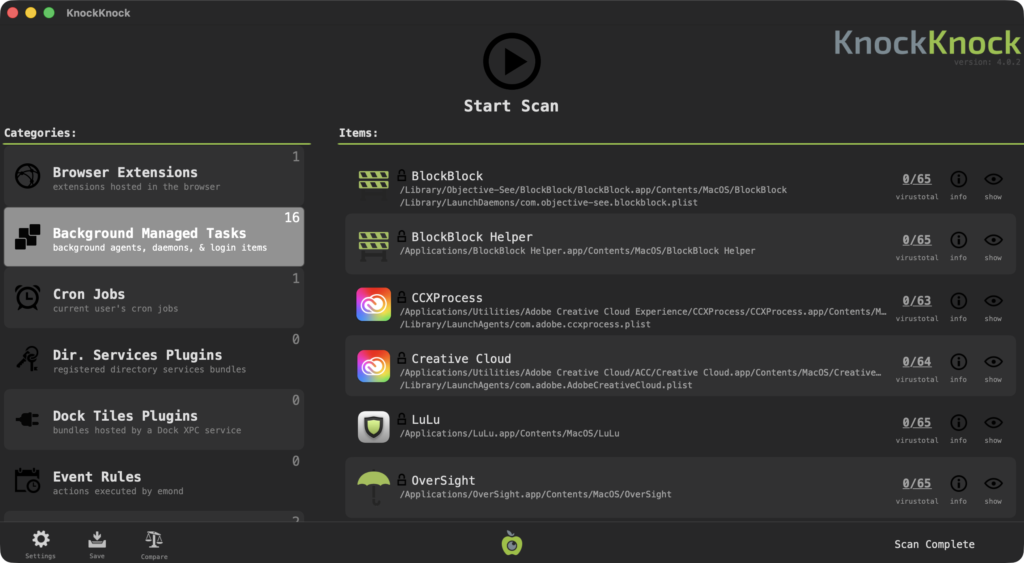
Download it from Objective-See’s website and run it in Safe Mode (hold Shift while booting). Safe Mode prevents rootkits from actively hiding themselves.
ESET Online Scanner for Mac
ESET offers a basic rootkit detector for Mac, but it’s limited and designed for older macOS versions. The current version scans for suspicious modifications in system files, but it’s not comprehensive.
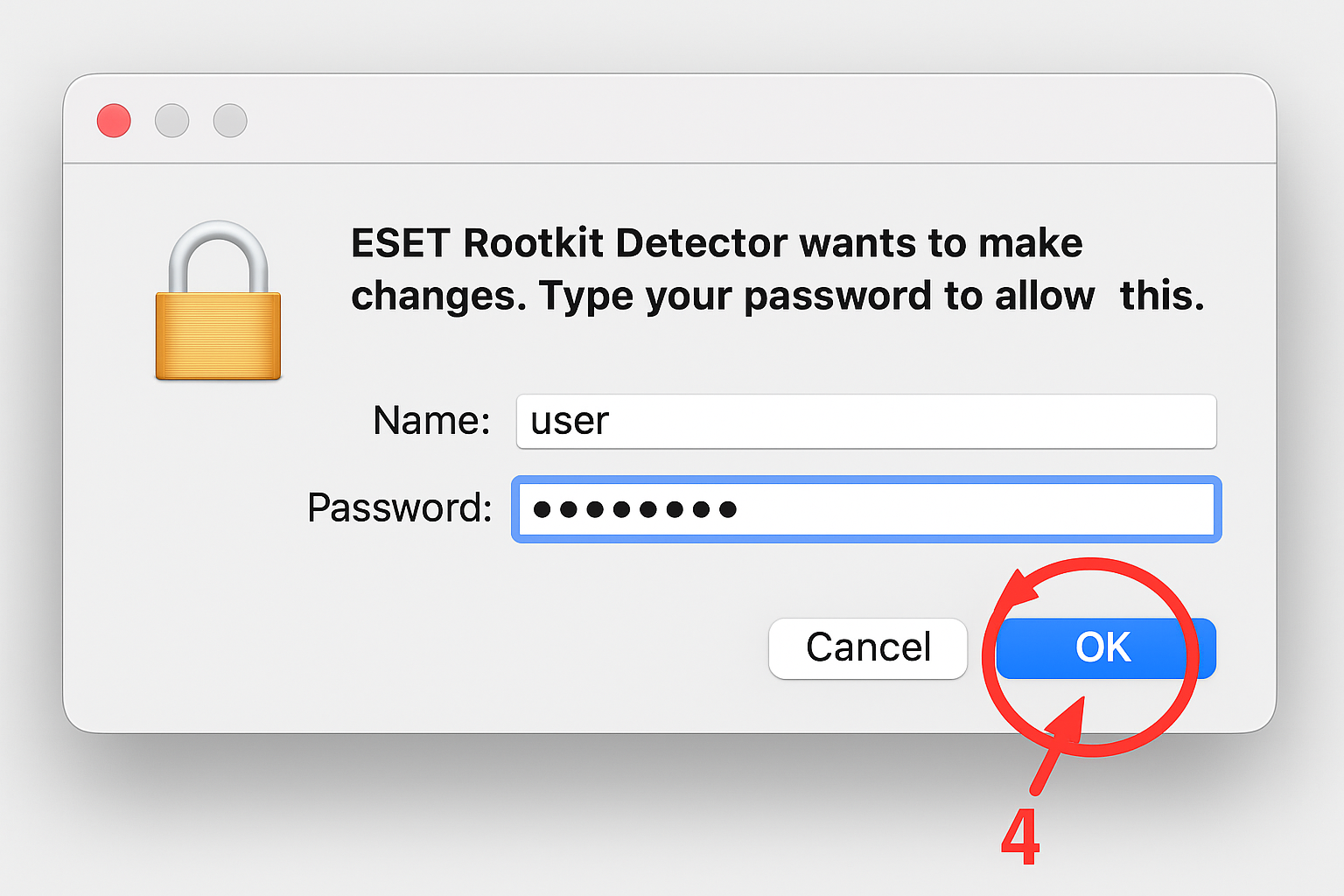
Better than nothing, but don’t expect Windows-level detection capabilities.
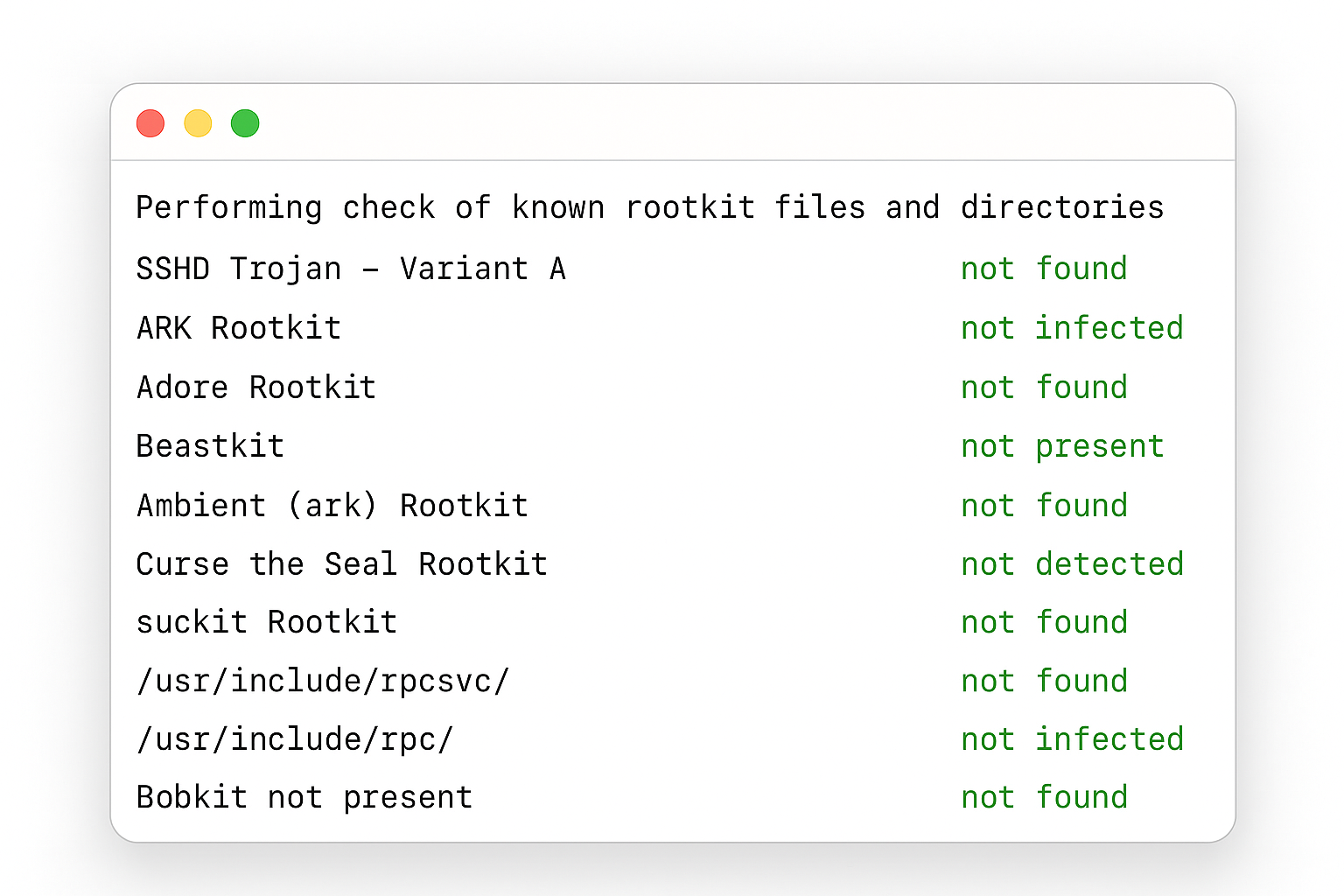
Why Linux Rootkit Detection Tools Don’t Work on Mac
You might find guides recommending Rootkit Hunter (rkhunter) or chkrootkit. These are Linux tools that technically run on macOS, but they generate false positives because they don’t understand macOS-specific behaviors.
If you want to try anyway, install via Homebrew:
brew install rkhunter
sudo rkhunter --check --enable all --disable none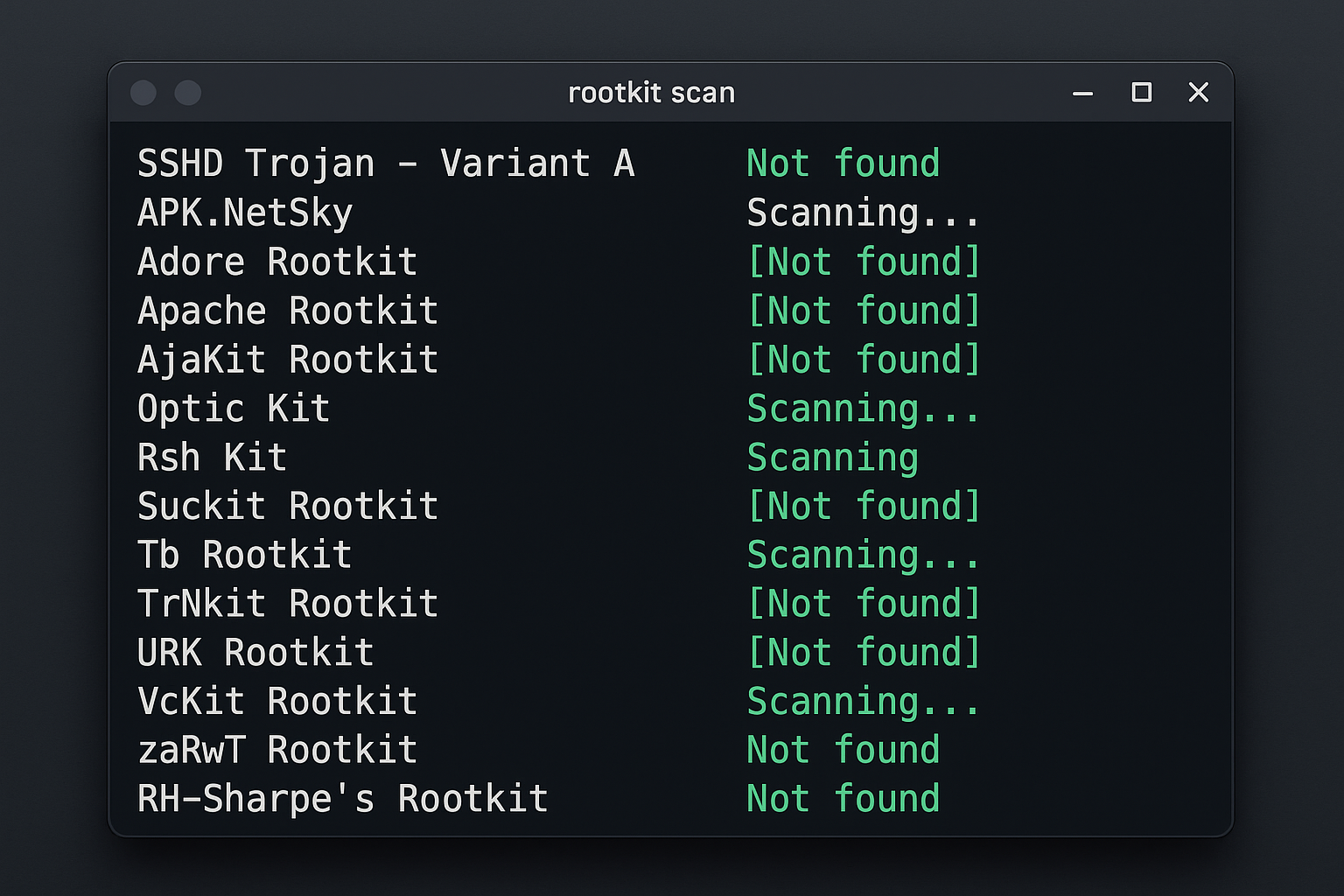
Just know that warnings about “suspicious” macOS processes are usually false alarms. These tools were never designed for Mac’s architecture.
Complete macOS Reinstall: The Nuclear Option (Which Actually Works)
Here’s what security professionals actually do when they suspect a rootkit: reinstall macOS.
I know that sounds extreme, but it’s the only reliable way to remove a rootkit that’s gained deep system access. Rootkits can manipulate the very monitoring systems designed to detect them, making removal tools unreliable.
If you suspect infection:
- Back up your data (scan it on another system first)
- Boot into Recovery Mode (
Cmd + Rduring startup) - Reinstall macOS from Recovery
- Restore your data carefully
This removes most rootkits because it replaces system files they depend on. If the rootkit infected firmware (rare but possible), you might need Apple’s help.
Mac Rootkit Prevention: Better Than Detection
Since detection is so limited on Mac, focus on prevention:

- Keep macOS updated automatically
- Don’t disable Gatekeeper or SIP (System Integrity Protection)
- Download software only from trusted sources
- Be suspicious of admin password prompts from unknown apps
The reality is that Mac rootkit detection isn’t where Windows detection was five years ago. Apple’s approach prioritizes prevention through system-level protections rather than after-the-fact scanning.
When to Contact Apple Support for Rootkit Issues
If you’re seeing persistent weird behavior after trying these steps, contact Apple Support. They can run diagnostics that aren’t available to consumers and help determine if you’re dealing with hardware issues, software conflicts, or actual malware removal.
It’s not the answer Windows users expect, but it’s the current reality of Mac security. The good news? Rootkits are still relatively rare on macOS compared to other platforms.
The bad news? When they do show up, your options are limited.
This whole situation is honestly a bit frustrating coming from the Windows world, but at least now you know what you’re working with. Keep your system updated, be cautious about what you install, and don’t hesitate to reinstall if something feels seriously wrong.
